Download Deceit

This is a public service announcement about a scam that recently affected a service we use, and even if you are not directly affected yourself, your friends or family could be. None of our business services were compromised.
Discord is a VoIP and instant messaging social platform. You can think of it as kind of a ‘Zoom for Gamer Geeks’ merged with chat messaging services like Facebook Messenger and Facebook Groups. Users set up niche groups for a particular interest, be that a shared hobby, a particular game, or a YouTube channel, communities which are referred to as “servers”. Many of the old message board forums have migrated to become Discord servers and there are well over 150 million monthly active users.
The scam involves a ‘hook’ conversation somewhere that a user frequents and appears to come from a known contact. The scammer clearly knew a lot about the account they were faking (Red) and were able to pitch well enough to fool the victim (Blue) into downloading and running the program on the link they provided.
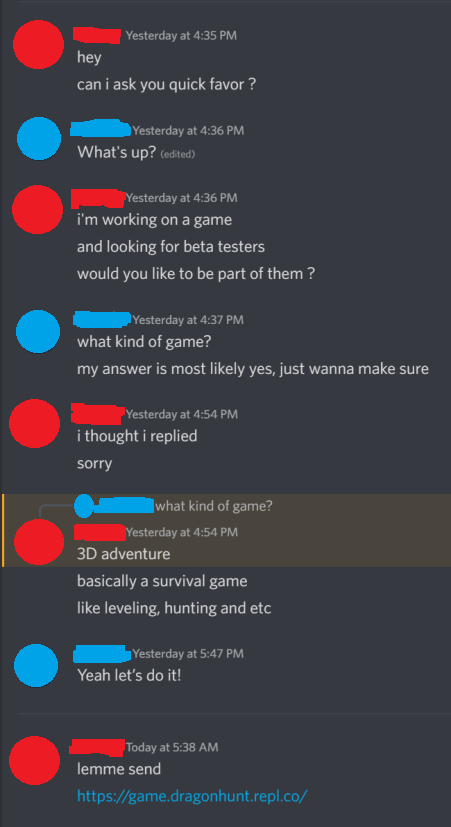
In the above case, Red was known to Blue and was known to be making games, so the request to test said game appeared legit on initial inspection. However, the content of the downloaded file was not a game that needed testing, but instead a piece of malware. It infected Blue’s account and began to send similar messages in an attempt to spread.
Blue explains what they experienced when Red took control of their account using the downloaded malware:
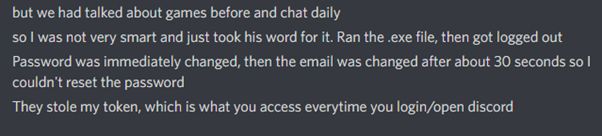
While Blue said, ‘I was not very smart’, given the information the scammer used, anyone could have been fooled. Then scammer was also particularly convincing in this case because they’d successfully stolen an account that belonged to a game creator, giving the pitch a veneer of legitimacy.
The .exe file used in the scam was a piece of malicious software called ‘Anarchy Grabber’ that steals and then fakes the ‘token’ that is created when Two-factor Authentication is successful, and uses this to login as the victim’s account, and then propagates the scam to further victims.
If you believe you or someone you know has been affected by this scam, this link can help. Solidarity IT can assist you in following these steps to recover your account.
https://www.reddit.com/r/discordapp/comments/lpmf6v/anarchygrabber3anarchygrabber_information/
Something we can all take away from this is to always double- or triple-check who is sending a program to you and what it does. Our ‘Take Control’ remote access software is single-use and requires either the exchange of a security code over the phone, or for you to be signed up to our Protect-IT contract for that machine, before we get access to work on your computer.
Broadly speaking, these kinds of scams are a common way to trick people into giving malicious users access to accounts and computers. It’s like getting past a locked door by tricking someone into handing over the key. If you have any further concerns about this or any similar attacks, just get in touch.


Leave a Reply