What Does Hacking Look Like?
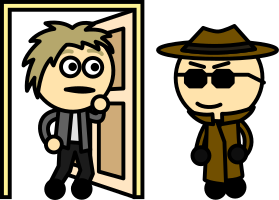
What does an online attack look like? We often think of online attacks as being all about advanced programs and hidden exploits in software. However, while that can be the case, often gaining access to a computer system works by tricking the user into allowing it. After all, you don’t need to pick the lock if you can con someone into opening the door for you.
Common examples of this include phishing emails, which are often designed to look like they’re from someone the user trusts and deceive them into clicking on a link or downloading software. These will insist that the requested action is urgent to fool the user into panicking, so they’ll act before taking the time to verify the authenticity of the email.
Another common trick is having infected accounts on Facebook send messages to contacts, with the intention of getting the target to click on a link. Often these will have some tempting or unnerving message to make the recipient want to click it, such as suggesting that the link is to a video taken of the user, or that the link leads to a leaked or scandalous video of a celebrity. When these links are clicked on, they can infect the user’s account. This leads to that account sending the message on to other users, thus propagating itself and giving the attacker access to more accounts.
Facebook also has the issue of ‘fun’ quiz posts, which ask questions such as someone’s first car or the name of their first pet. These are designed to trick people into posting the answers to their account recovery questions, enabling an attacker to use this information to get into an account.
A variation on this is a post that asks what a person’s name would be if they were a wolf, Jedi, rockstar, superhero, or the like, where there’s a common pattern to names. Either they are based on information used for security questions or on a person’s date of birth, which is often used to prove identity, especially when trying to recover an account.
Generally, it’s a good idea to watch what links you click on, and what personal information you’re giving out online. Since these kinds of attacks are widely distributed, they don’t need to affect any specific individual, just to send enough out that eventually, someone somewhere will make a mistake.


Leave a Reply